Of all the ways a college student can find trouble, at least Ralph Barclay started in the library.
It was 1960, and he was wandering through the engineering library, then on the third floor of Holland, when his eye was drawn to a freshly minted Bell Systems Technical Journal. Inside, amid some positively mind-numbing treatises, he found the article, “Signaling Systems for Control of Telephone Switching.”
Years later, this one article would be referred to as “the keys to the kingdom,” a plain-spoken description of how the phone system evolved and, unbeknownst to the authors, the means by which an 18-year-old electrical engineering student from Soap Lake could hack into its inner workings.
“I thought, ‘This is way better than using a pay phone,’” Barclay, who died in 2009, recalled to Phil Lapsley, author of Exploding the Phone: The Untold Story of the Teenagers and Outlaws Who Hacked Ma Bell. “…this is a way to get around all that other stuff and do it directly.”
That “it,” Lapsley adds, “was making free calls.”
Lapsley writes that Barclay figured this out by gleaning several insights from the journal. The first, and perhaps biggest, was that a 2,600 Hz tone in the telephone line reset a remote switch. The journal, now shelved on the top floor of the Owen Science and Engineering Library, has the number “2,600” underlined, in pen, possibly by Barclay, or possibly by one of the legions who sought out the article in his wake.
The 2,600 Hz tone also let one reroute a call to most anyplace. And because billing was based on a local switch unaffected by the tone, these calls were now off the books.
The thrill of a free phone call seems quaint by today’s standards, when one can talk internationally for as little as a penny a minute, or get a cell phone with unlimited domestic long distance. To be interviewed for this story, Lapsley called Pullman over Skype for free from Bangalore, India.
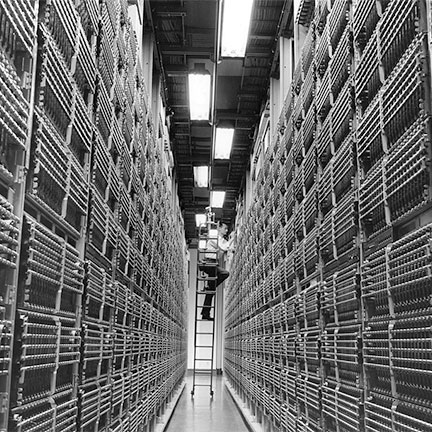
But Lapsley calculates that in the mid-1950s, when the first known “phone phreaker” hacked into the system, a ten-minute long-distance call from Miami to Denver cost $5.90. That, he says, comes to $48 in today’s dollars. Worming one’s way into the phone network had an added appeal for Barclay, who grew up tinkering with telephones and radios: He could now play with the largest machine in the world.
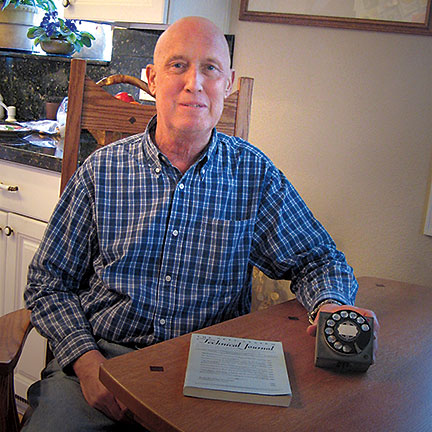
Within weeks of reading the journal article, Barclay put together a nine-volt battery, a rotary dial, and a single transistor oscillator circuit that could make the 2,600 Hz tone. It worked, but inconsistently, as AT&T, also known as Ma Bell, was converting to a system in which phone digits were represented by multiple frequencies, not the single frequencies of Barclay’s first creation. Over the coming months, he built a more sophisticated box that included a touch pad he made from a mechanical Burroughs adding machine. He housed it in a metal box that happened to be painted blue.
From then on, this device would be called “the blue box,” with its status elevated by the 1971 Esquire article, “Secrets of the Little Blue Box.” Steve Wozniak and Steve Jobs built and sold the box, and both said it led to their founding Apple Computer. As far as anyone knows, and as AT&T later asserted in a memo obtained by Lapsley, Barclay’s blue box was the first.
Barclay used his blue box to make an occasional personal call, help friends call home for free, and mostly, he told Lapsley, “to see where we could call.”
The following summer, while working in a radio and television repair shop in Ephrata, he took to calling farther and wider as a friend whose dad worked for the phone company gave him a book operators used to route calls.
The fun ended with the summer, when he was arrested and charged with bookmaking, possibly because a friend who often used the phone talked a lot about horses. The charge was reduced to making a phone call without paying for it, a misdemeanor. At his trial, the judge recalled freezing water in the shape of nickels to make long-distance calls from pay phones. He gave Barclay a suspended sentence, and Barclay’s phreaking days were over.
His widow, Trudy Boardman, says he went on to have a prosperous career with a video and broadcast technology firm, as well as a company he launched himself.
“He was just a curious guy who saw this article in a technical publication and decided to mess with it,” she says.
Curiosity seems to have been a hallmark of many early phreakers, says Lapsley.
“Some of it is just being nosy and being curious, being open to new things,” he says. “A second thing, which is harder to describe, is a lot of people who are involved in either computer security or any other kind of security have their brains wired in a particular way that they notice vulnerabilities and they see things that, for lack of a better word, normal people don’t see. They look at something and they immediately think, ‘Well gosh, this is a vulnerability.’”
That has some clear downsides in the later phreakers, many of whom had more nefarious and mercenary interests, as well as many modern-day hackers following in their footsteps.
Michael Quinn (’83 PhD Computer Science), author of Ethics for the Information Age and dean of the Seattle University College of Science and Engineering, sees a downside to Barclay’s curiosity and thrill with the technical challenge of the blue box.
“He did make use of his invention,” Quinn says in an email, “and I imagine he got a lot of satisfaction and gained prestige by helping his friends call home for free. I believe Mr. Barclay’s actions were unjust (and therefore wrong) because he deprived AT&T of what it was due: being paid for the use of its long-distance telephone network.”
For his part, Lapsley looks at Barclay’s “fundamental motivation,” which “was not to rip anybody off. The fundamental motivation was, ‘Hey, look at this amazing network that we can play with and learn about…. I look at that and find it very difficult to get real worked up from a loss or damage or evil perspective.”